Technical Designs Impacting the new Playing Globe in the 2024
Blogs
Utilizing rules including entanglement and you will superposition, quantum cryptography offers unbreakable security along with the features the real deal-day eavesdropping recognition. The authorities may need adjust its decoding ways to avoid criminals playing with asymmetric encoding. Whether or not quantum computers have not yet , hit maturity, search on the article-quantum cryptography could have been booming, supported by enhanced funding inside their invention.
The best black colored-jack is found in four high-restrict salons to the part of the Eliminate. Play the online type of Solitary-platform Black-jack, with simple handle to own punctual-swinging gaming step. Continue greatest monitoring of the fresh cards with just you to definitely patio on the enjoy, and create profitable methods to overcome the new agent. This enables advantages to help you quit the render and also you can also be see half of their options back before the specialist inspections to possess blackjack.
] Constantly, such as sites give economic bonuses just in case you safe her or him and you will incorporate some kind of an evidence-of-risk otherwise facts-of-works formula. The brand new KuppingerCole research protection systems statement now offers information and you can guidance in order to find delicate study security and you can governance products which finest see subscribers’ demands. After that, Gubsheep’s imaginative access to blockchains and state-of-the-art cryptography not only produces for a more intriguing and advanced playing sense, and also diversifies the methods where this type of innovation might be made use of beyond its latest, popular financial services. Indeed, MIT Technical Remark notes that games could even be seen since the a revolutionary action to your building and you may hosting steeped the fresh, shared decentralized metaverses you to definitely no one is the owner of, and no it’s possible to avoid. Produced by MIT graduate Brian Gu beneath the pseudonym Gubsheep, Dark Forest is the community’s very first decentralized unfinished-guidance video game, and possibly more state-of-the-art software to the blockchain.

To laymen, the guidelines governing quantum mechanics will likely be hard to know and you will photo, however, quantum online game offer a concrete and you can entertaining means to fix mention her or him. Such as complete greeting offers straight down entryway traps rather, providing beginners to try freely across the individuals game groups instead worry of economic losings initial, if you are learning the working platform’s diverse amusement possibilities. Equity stays a center concept because of it designer, which makes them dedicate significantly in the maintaining tight RNG qualifications.
The ethos away from invention, integrity, and user-centric design will continue to inspire generations from games designers and operators the same. The fresh energetic directory of Quantum Secret Shipping (QKD) is restricted to help you one hundred–200 kilometer because of photon loss and decoherence in the fiber optic cables. Quantum repeaters, designed to extend QKD over long distances, stay-in the new experimental stages and you will deal with demands including mistake correction and you may entanglement distribution.
Nu Quantum shines in the domain of fabricating quantum photonic gizmos to have safer communications. Its dedication to carrying out solitary-photon source and you can detectors especially for quantum secret shipping shows their commitment to the fresh evolution from cryptographically safeguarded communication. Having a keen unwavering work at quantum-secure encoding services and products, Qrypt can one observe, especially with its advanced quantum-safer security platform, Qryptal. Teaming up with technical and you will shelter monsters, their worldwide arrive at allows deploying reducing-line quantum-secure possibilities which can be both necessary and you may searched for in several opportunities. MagiQ Tech integrate an excellent quantum haphazard amount generator in its items, focusing on the importance of unconditional shelter centered on quantum legislation and you can positioning in itself while the a vital athlete inside the quantum security systems. Quantum cryptography is short for a great paradigm move within the secure communication, leveraging the fresh instructions from quantum auto mechanics make it possible for secure study signal.
How could a real-industry quantum communications program transmitted suggestions?
- To fight so it, organizations will need profile for the in which this type of formulas are used and make certain they can decrypt and test all the analysis moving due to the business communities.
- Partnerships that have including enterprises since the Universal , Vital, or any other news beasts has welcome these to release game lower than personal rights such Braveheart, Forrest Gump, and Ferris Bueller’s Time Of, yet others.
- Immediately after submitted, the info in every offered take off can not be altered retroactively as opposed to the change of the many next reduces, which means collusion of your own circle majority.
- Symmetrical encryption is often common to own providing large amounts of information since it is reduced computationally rigorous than simply asymmetric tips.
- Comprehensive open instructional look on the cryptography is fairly previous, beginning in the fresh mid-seventies.
- Cryptologic shines off their on-line casino software business by providing ample earnings, an array of online game, and you may consistent gameplay.

If a third party accesses the fresh decrypted analysis, they could very likely use it to have financial profit, impersonation, or any other methods to see a reward https://happy-gambler.com/copy-cats/real-money/ . Which advantageous asset of elliptic contour cryptography causes it to be really rewarding to have doing cryptographic computations inside a resource-constrained environment such safer aspects that is available to your smart notes otherwise inserted in different devices. Asymmetric cryptosystems considering elliptic curves have many software within the stuck cryptography. They are utilised to own IMSI encryption within the 5G SIMs, and in passports to have common verification amongst the processor chip plus the viewer. An excellent symmetrical algorithm is viewed as safe provided no cryptanalytic means might have been identified which can discover magic key shorter than simply by exhaustively analysis all you are able to keys. The appearance of a new algorithm is always based on a great blend of some other techniques created by cryptologists so you can parry in past times recognized attacks.
Such primitives provide simple characteristics, that are familiar with produce more complicated equipment named cryptosystems otherwise cryptographic standards, and this make certain a minumum of one highest-height defense characteristics. Notice, but not, that the difference in cryptographic primitives and you will cryptosystems, is pretty random; such, the new RSA algorithm is frequently sensed a cryptosystem, and sometimes an excellent ancient. Regular types of cryptographic primitives is pseudorandom characteristics, one-way characteristics, an such like. Just as the growth of digital servers and you can electronics assisted inside cryptanalysis, they made possible much more advanced ciphers. Furthermore, machines invited to the encoding of any kind of data representable in almost any binary format, as opposed to ancient ciphers which simply encrypted authored words messages; it was the newest and extreme. Computer system have fun with has therefore supplanted linguistic cryptography, both for cipher design and cryptanalysis.
App
Currently, you can find at the least four form of blockchain networks — social blockchains, personal blockchains, consortium blockchains and you may crossbreed blockchains. Bitcoin or any other cryptocurrencies already safer its blockchain because of the requiring the fresh records to incorporate evidence of performs. If you are Hashcash was created within the 1997 by Adam Right back, the initial tip was proposed by the Cynthia Dwork and Moni Naor and Eli Ponyatovski in their 1992 paper “Cost via Processing otherwise Combatting Pre-approved offers”. Consider the shelter vulnerability from a database out of kept checking account passwords. Anyone with possibly registered otherwise unauthorized access to the financial institution’s computers you will potentially understand the password. Individual important factors will be common both because of a formerly founded safe communication station such a private courier or secure range or, a lot more almost, a secure trick change strategy for instance the Diffie-Hellman secret arrangement.
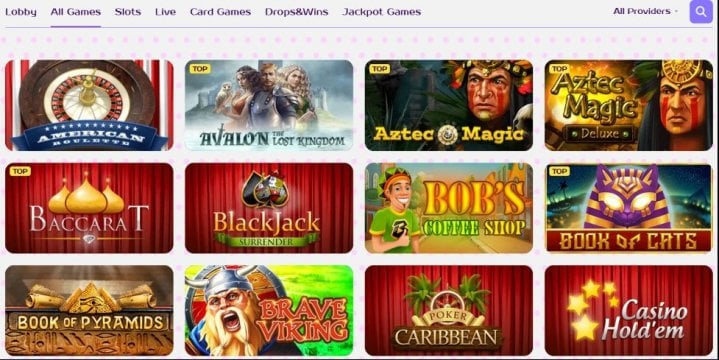
Very performant and you may affiliate-friendly, Cryptologic ports continue to be among the most sought-once video game from the online domain. For on line position followers looking to gamble real cash harbors, gambling enterprises offering Cryptologic harbors render a promise of brilliance and value, making sure an enjoyable and you will fulfilling gambling sense. All of the gambling enterprises playing with Cryptologic’s app concur that its video game program is straightforward and simple to make use of. The new gambling games will be accessed without difficulty from the casino’s inside-website search engine which includes of numerous answers to flick through the brand new games. The new video game are demonstrated inside a simple seeing style otherwise thanks to thumbnail viewpoints which comes that have an initial description of the games and its laws in advance to play. Cryptologic now offers its users totally free game models just before to try out to have real cash.
The info-inspired information and you will expertise that i has wanted to companies are a switch reason behind direction conclusion to the several domain names in addition to revenue maximization, rates optimization, cash leakages, fraud avoidance, costs and you can consumer conduct. Within the 2025, perhaps one of the most alarming trend in the cybersecurity will be the increasing access to multivector attacks and multistage means. Cybercriminals control a mixture of ideas, techniques and functions (TTPs), striking around the multiple parts immediately so you can infraction defenses. We’ll discover a rise in elegance and evasion away from net-dependent symptoms, file-founded periods, DNS-founded symptoms and ransomware symptoms, to make it more difficult to possess old-fashioned, siloed security devices so you can effectively reduce the chances of progressive dangers. QuintessenceLabs try driving the fresh borders featuring its work with quantum interaction technology.
An upswing of quantum computing presents a life threatening hazard so you can current encoding strategies and cybersecurity possibilities. Modern cryptosystems are made to withstand the potential measuring electricity out of old-fashioned computers, which could only require various to help you thousands of many years so you can effectively brute-push attack today’s cryptographic formulas. Use times for quantum-unwilling and you may article-quantum cryptography try as numerous as the cryptography have fun with circumstances is actually as a whole. Which guide examines the newest dynamically developing areas of quantum measuring and you may quantum cryptography.
Analysis Ethics
Banking institutions and financial institutions apply quantum key shipment (QKD) so you can safe correspondence, making sure purchases and you may customers study are protected from quantum-calculating periods. So it reducing-line method is crucial to own keeping believe and you will stability inside financial system, guarding against prospective breaches that will cause big monetary losings. IBM cryptography possibilities blend innovation, asking, possibilities consolidation and you will handled security functions to simply help make sure crypto agility, quantum-shelter and you will solid governance and risk regulations. Away from symmetrical to help you asymmetric cryptography in order to hash functions and you can beyond, make certain research and you can mainframe shelter having end-to-end encryption custom-made to satisfy your organization needs. So it book explores the basic principles out of quantum measuring and its apps within the codebreaking and hacking, and actions and you may technology to possess defending options against quantum episodes. They combines leading professionals away from across academia and industry in order to render an intensive review of the newest influences out of quantum computing on the cybersecurity and cryptography.

Guaranteeing the newest credibility away from sent and you may obtained data is a significant intent behind cryptography used in performing the manners of organization, authorized by using electronic signatures. As a result of asymmetric cryptography, files might be revised which have electronic signatures, that will just be produced by using an exclusive trick. Receiver out of digitally closed data files may use the brand new sender’s societal the answer to make sure the brand new signature’s authenticity and you may confirm that the newest document has not been interfered with through the signal.
